Does NB iot module need a sim card?
The simple answer is needed.
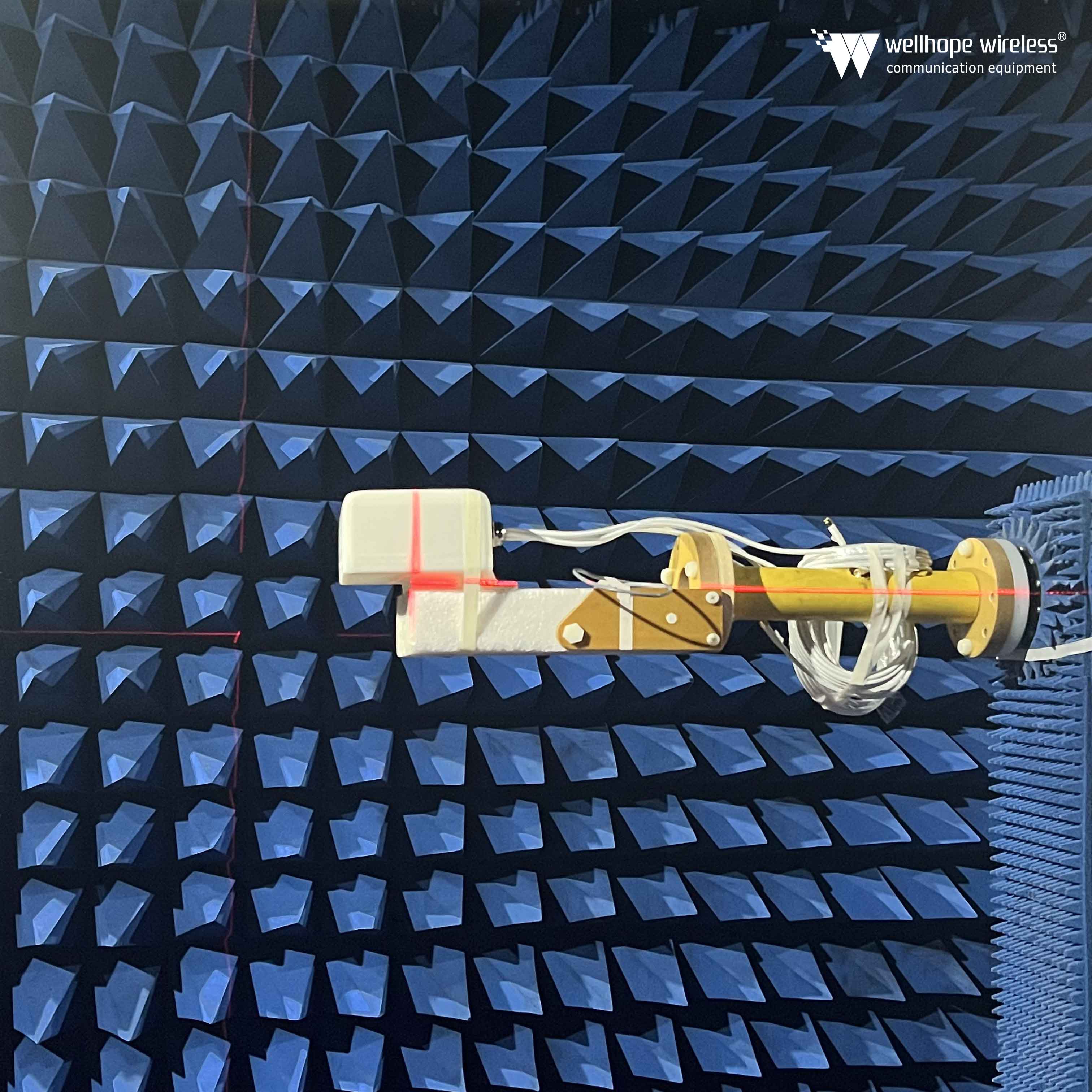
(More wireless communication knowledge; IoT knowledge, antenna cable https://www.whwireless.com )
NB iot is deployed under the signal coverage of the existing cellular network and uses the licensed frequency band, so it can only be used through the network provided by the operator. Someone may ask why lora, which is also a low-power wide area network, can not use a sim card, while nbiot has to use a sim card? This is still related to the network frequency bands used by the two networks.
NB iot devices do not need a gateway, and they rely on 4G coverage and use the spectrum in LTE, so NB-IoT is not easy to work in remote areas without 4G signals. Lora uses an unlicensed frequency band, which means that there is no frequency band operated by an operator. Therefore, Lora needs to pass through a gateway during use.
NB-IoT network
The NB-IoT network is shown in the figure. It can be seen that it consists of 5 parts:
NB-IoT terminal. As long as the corresponding SIM card is installed, IoT devices in all industries can access the NB-IoT network;
NB-IoT base station. It mainly refers to base stations that have been deployed by operators, and it supports all three deployment modes mentioned earlier;
NB-IoT core network. Through the NB-IoT core network, the NB-IoT base station can be connected to the NB-IoT cloud;
NB-IoT cloud platform. The NB-IoT cloud platform can process various services and forward the results to the vertical business center or NB-IoT terminal;
Vertical business center. It can obtain NB-IoT service data and control NB-IoT terminals in its own center.
Compared with the transport layer in the traditional IoT, NB-IoT changes the complex network deployment, in which the relay gateway collects information and feeds it back to the base station. Therefore, many problems such as multi-network networking, high cost and high-capacity batteries are solved. A network throughout the city can bring convenience to maintenance and management, and can easily solve and install advantages by separating it from property services. However, there are new security threats:
Access to high-capacity NB-IoT terminals
One sector of NB-IoT can support connections with approximately 100,000 terminals. The main challenge is to perform effective authentication and access control on these large-scale real-time high-volume connections to avoid malicious nodes from injecting false information.
Open network environment
The communication between the perception and transport layer of NB-IoT is completely through the wireless channel. The inherent vulnerabilities of the wireless network bring potential risks to the system. That is, an attacker can transmit interference signals to cause communication interruption. In addition, because there are a large number of nodes in a single sector, an attacker can use nodes controlled by him to sponsor a denial of service (DoS) attack, so he can affect network performance.
The solution to the above-mentioned problem is to introduce an effective end-to-end authentication mechanism and key agreement mechanism to provide confidentiality and integrity protection and information legality identification for data transmission. Currently, computer networks and LTE mobile communications have related transmission security standards, such as IPSEC, SSL and AKA. However, the main problem is to implement these technologies in the NB-IoT system through efficiency optimization.
On the other hand, a complete intrusion detection and protection mechanism should be established to detect illegal information injected by malicious nodes. Specifically, first, a series of behavior profile configurations should be established and maintained for certain types of NB-IoT nodes. These configurations should of course describe the behavioral characteristics of the corresponding nodes during normal operation. When the difference between the current activity of an NB-IoT node and its past activity exceeds the threshold of the item in the configuration file configuration, the current activity will be regarded as an abnormal or intrusive behavior; the system should intercept and correct in time to avoid Various intrusions/attacks have adverse effects on network performance.
www.whwireless.com

















 News
News